Thoughts on Synthetic Fingerprint Sites
Users often visit fingerprint checker sites to verify their browser configuration:
These sites are useful for checking specific fingerprint values, but their ratings and scores often confuse users. Here's how to interpret the information they provide.
The false positive problem
Many warnings on these sites are false positives - alerts that suggest problems where none exist. These checkers use detection algorithms that don't reflect how real websites actually verify browsers.
Most of our customers we speak with test fingerprints on these sites, but even if they don't get a perfect result, they test it against their main use-case and that works more often.
The key insight: Real-world success matters more than synthetic scores. If your profiles work on actual target websites, the fingerprint is effective.
Why false positives happen?
Fingerprint checker sites rate configurations against narrow assumptions about "normal" browsers. They often flag legitimate variations as suspicious:
- Regional language settings that don't match their expected patterns
- Browser extensions that modify certain values
- Legitimate browser versions they haven't updated in their database
- Privacy-focused browsers like Brave that intentionally differ from Chrome
Real examples
Test this yourself: Open these checker sites with your regular, unmodified browser. You'll likely see warnings even though you're using a genuine setup.
Common false positives include:
- "Language mismatch" warnings on legitimate regional configurations
- "Platform inconsistency" alerts on standard browser setups
- "Outdated browser" warnings when you're already running the latest version
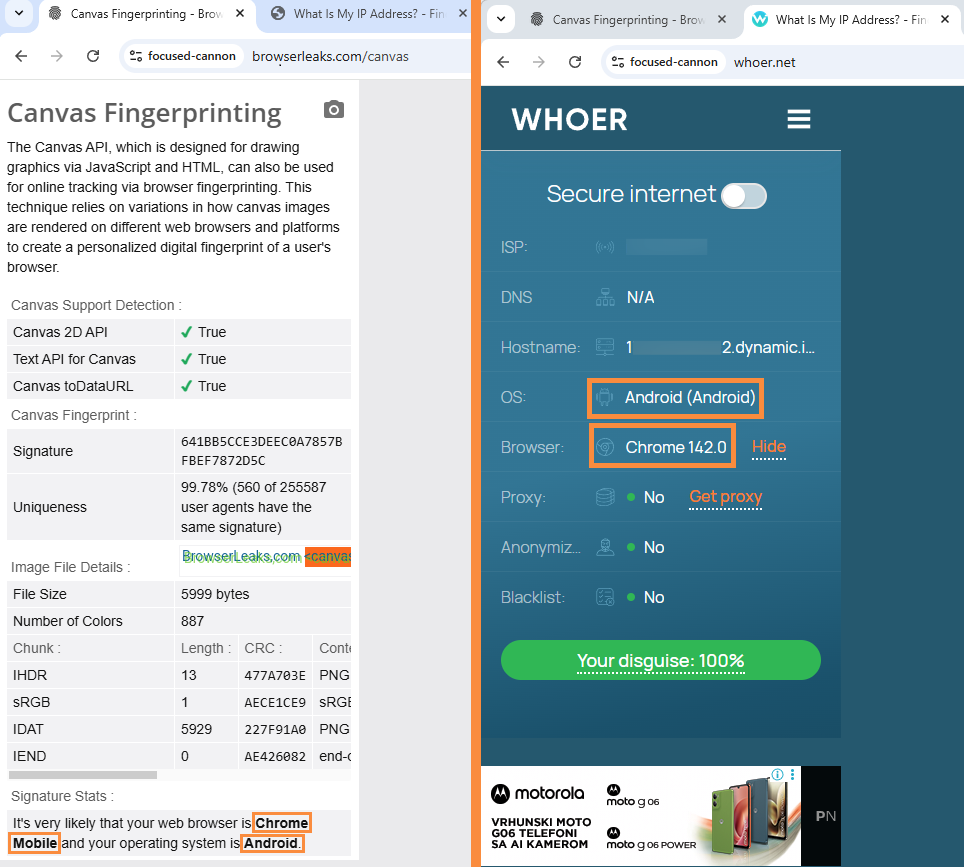
- Canvas warnings on privacy browsers that intentionally add noise
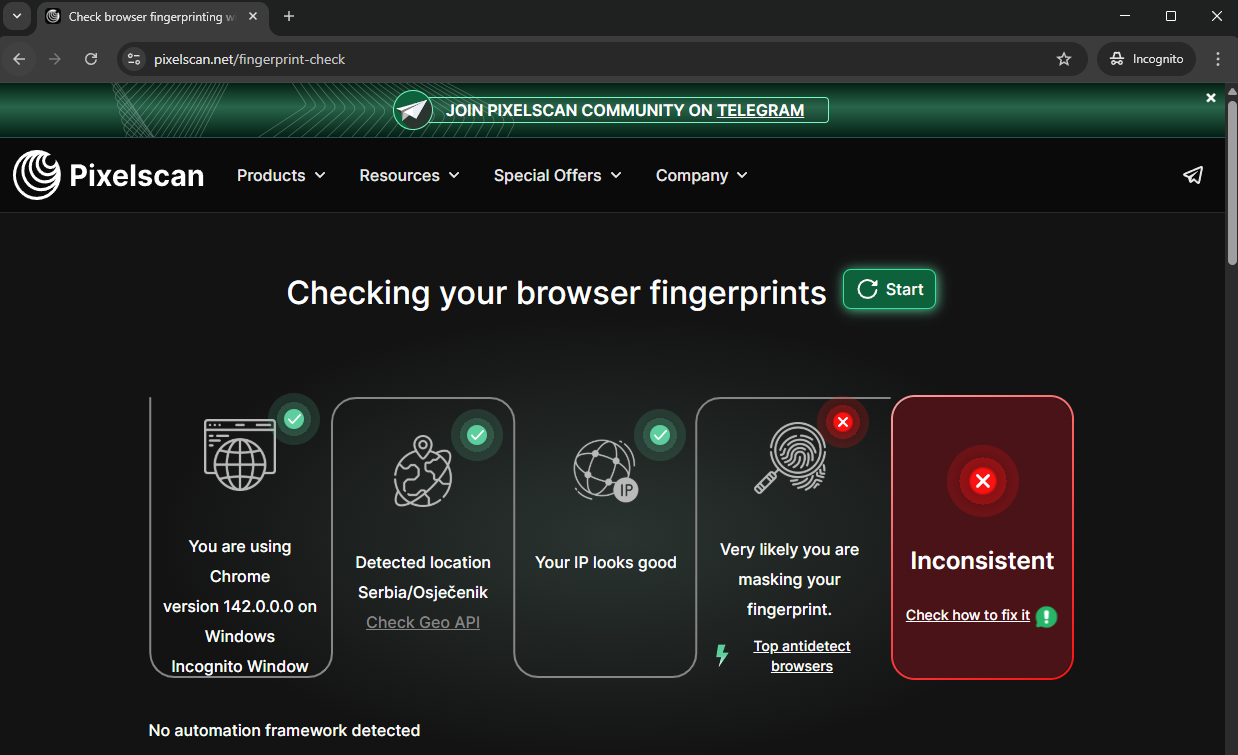
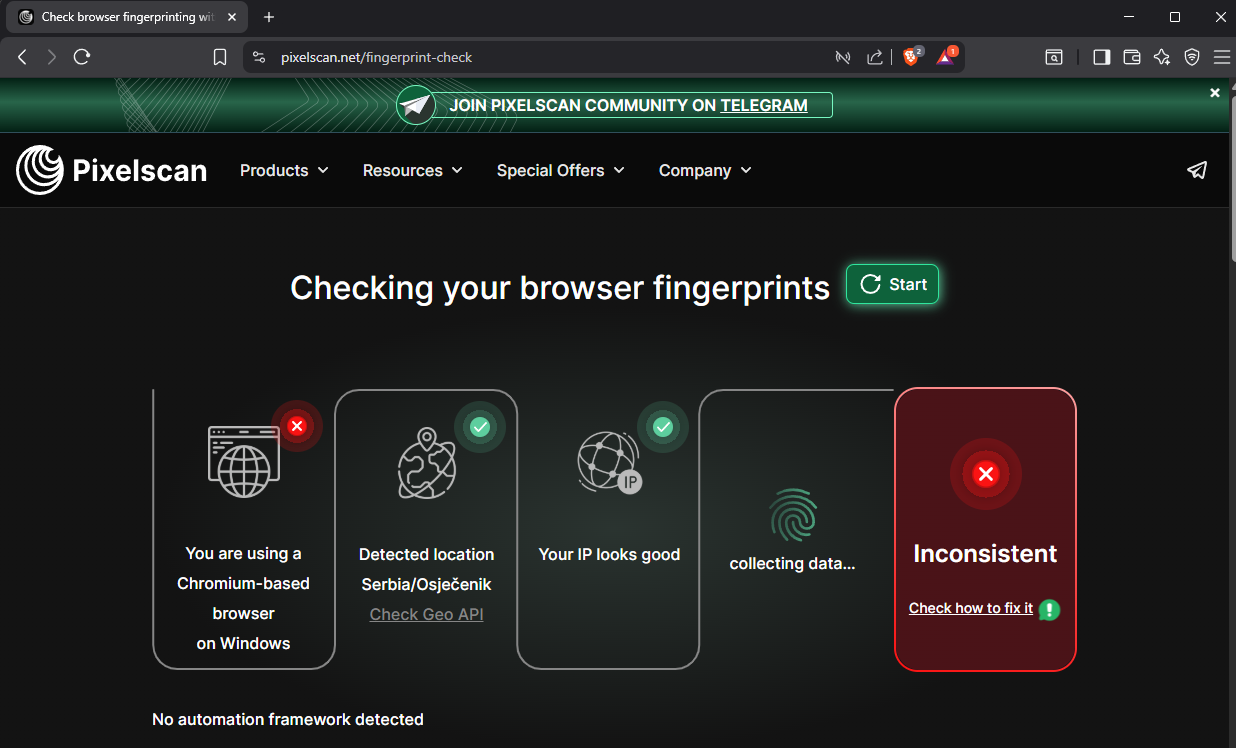
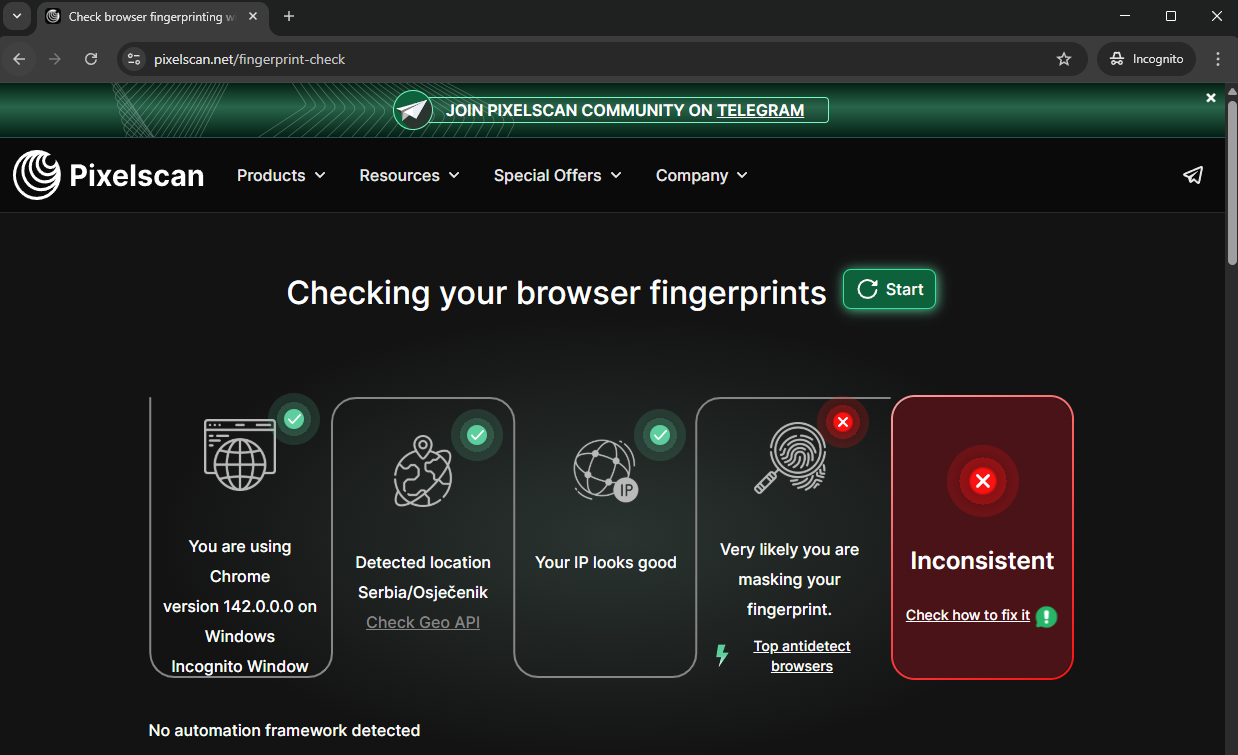
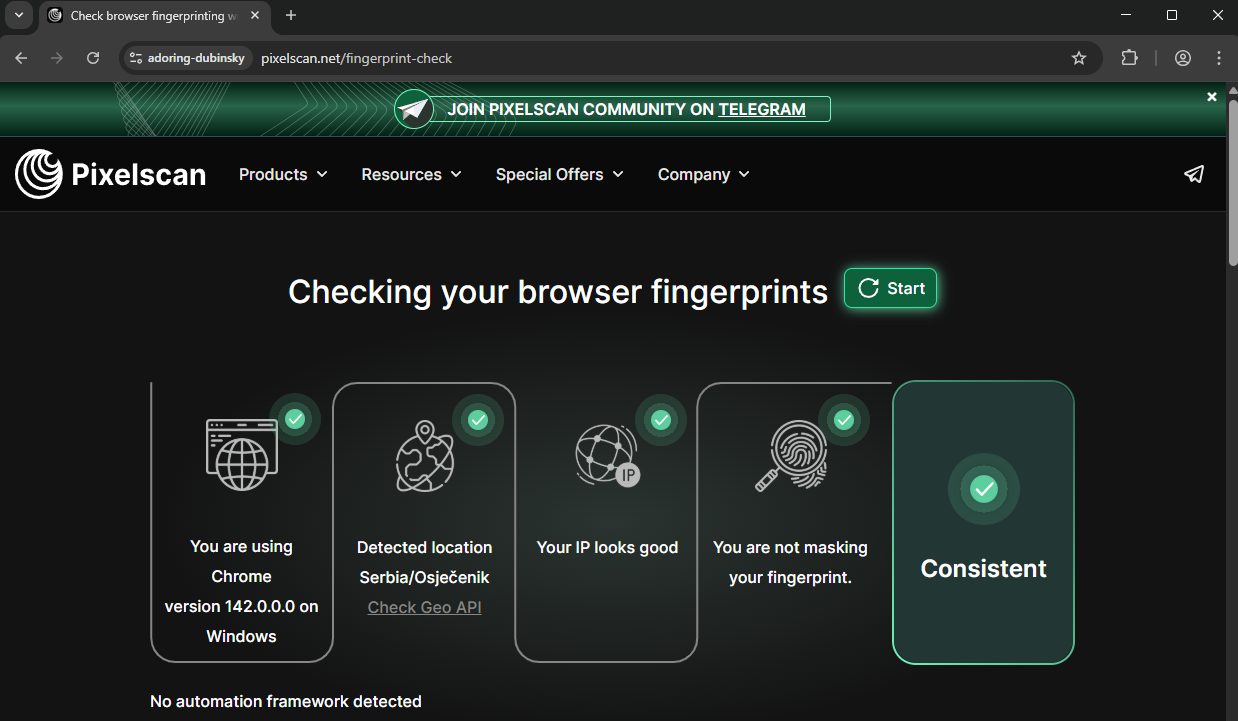
Here are multiple genuine browsers being flagged:
-
- Chrome -
-
- Brave -
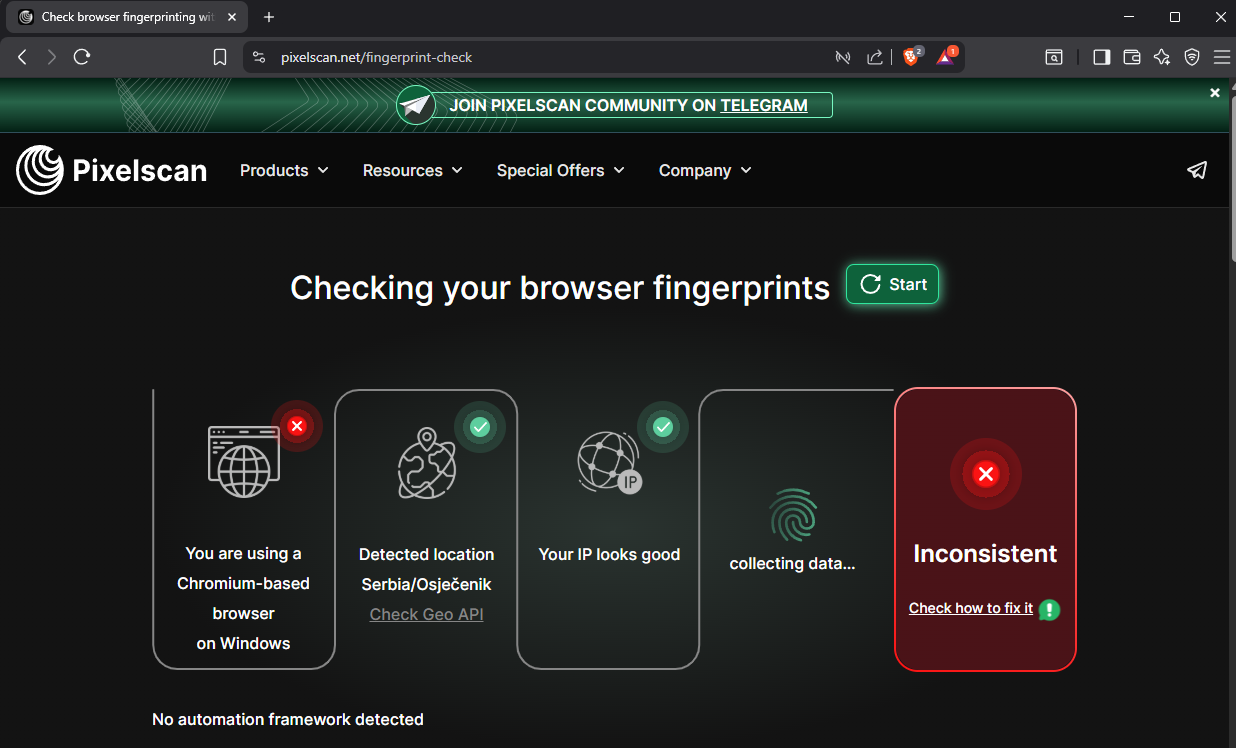
Even if your anti-detect browser performs perfectly on the synthetic test sites, it worth testing them on your real use case.
How Kameleo fingerprints work
Kameleo fingerprints are harvested from real devices and browsers. They contain natural variations that exist in actual user environments. These variations sometimes trigger simplistic detection algorithms, but they're precisely what makes the fingerprints authentic to real security systems.
Synthetic checkers often give perfect scores only to artificially generated fingerprints created by their own tools - the same fingerprints that real bot detection services can easily identify.
What actually matters
Focus on these factors instead of synthetic scores:
Success on target websites - Does your profile work on the actual sites you need to access? This is the only metric that matters.
Consistency - Do all your fingerprint parameters align logically (language, timezone, location, proxy)?
Appropriate tools for testing - Use checker sites to verify specific values, not overall "ratings":
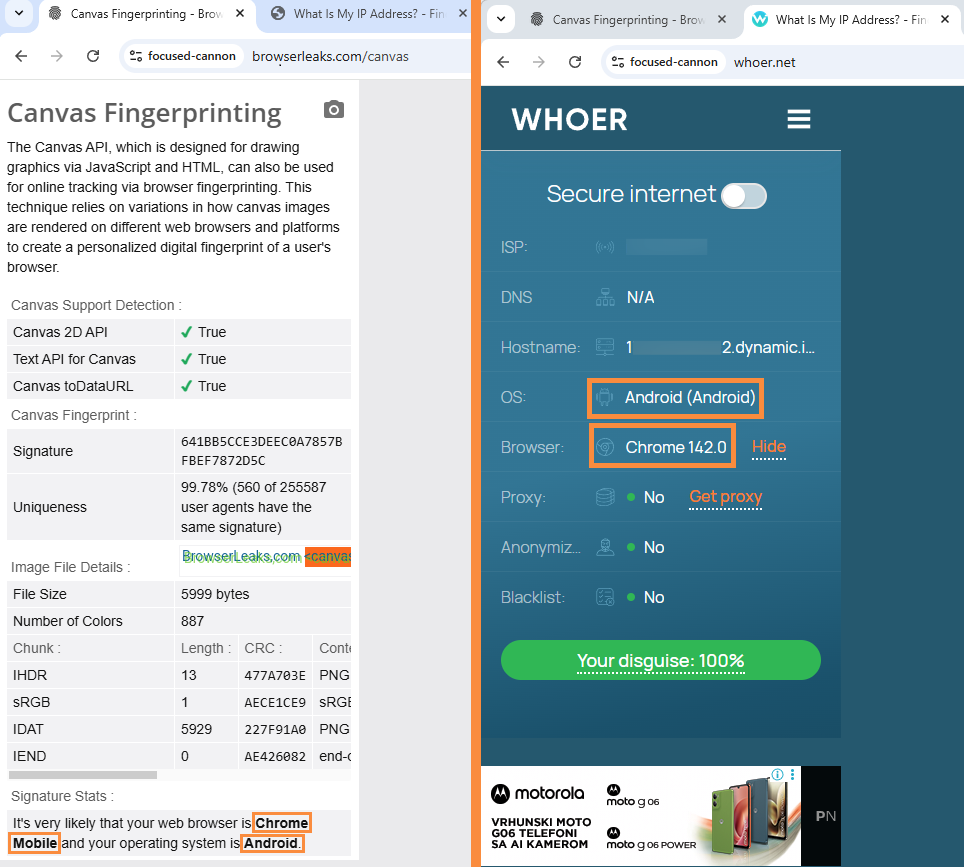
- whoer.net - Good for checking IP, timezone, and WebRTC leaks
- browserleaks.com - Excellent for detailed canvas testing
-
pixelscan.net - Useful for comprehensive fingerprint breakdown
Best practices
- Don't chase perfect scores on checker sites. They don't reflect real-world detection.
- Test on actual target websites to verify your profiles work where it matters.
- Use checker sites as diagnostic tools to verify specific values (Timezone, WebRTC, Canvas), not as pass/fail tests.